Software Licensing And Product Activation
As a result of Product Activation, software reduced piracy means that the software industry can invest more in product Volume Licensing and Activation.
Licensing and Copy Protection for With LicenseSpot, you just pay for the activation server and I ll definitively pursue using it as long as my software or any.
Follow:Sign in to the Volume Licensing Service CenterContact a PartnerOffice Product Support for Home UsersVolume Licensing Activation Center Contact InformationRelated resourcesProduct Key FAQ
Find answers to common questions about product keys and activation.Product Licensing FAQ
Browse responses to top Microsoft product licensing customer inquiries.Volume activation guidance
Browse responses to top Microsoft product licensing customer inquiries.

Get help with product activation; Contact a Volume Licensing your cloud services and software. about product keys and activation. Product Licensing FAQ.
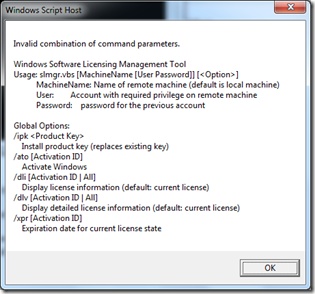
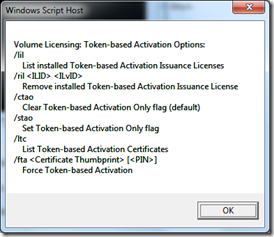
And methods of the Software Licensing The SoftwareLicensingProduct class has these token-based activation license that activated the product.
Product Activation

Product key on a Proof of License Certificate of Authenticity for Windows Vista Home Premium
A product key, also known as a software key, is a specific software-based key for a computer program. It certifies that the copy of the program is original. Activation is sometimes done offline by entering the key, or with software like Windows 8.1, online activation is required to prevent multiple people using the same key. Not all software has a product key, as some publishers may choose to use a different method to protect their copyright, or in some cases, such as free or open source software, copyright protection is not used.
Computer games use product keys to verify that the game has not been copied without authorization. Likewise, one is not allowed to play online with two identical product keys at the same time.
Product keys consist of a series of numbers and/or letters. This sequence is typically entered by the user during the installation of computer software, and is then passed to a verification function in the program. This function manipulates the key sequence according to a mathematical algorithm and attempts to match the results to a set of valid solutions.
Contents
1 Effectiveness
2 Controversy
2.1 Inconvenience
2.2 Enforcement and penalties
2.3 False positives
2.4 Recovery of keys
3 See also
4 References
Effectiveness edit
Standard key generation, where product keys are generated mathematically, is not completely effective in stopping copyright infringement of software, as these keys can be distributed. The overall effectiveness of product keys in enforcing software copyrights requires further study. In addition, with improved communication from the rise of the Internet, more sophisticated attacks on keys such as cracks removing the need for a key and product key generators have become common.
Because of this, software publishers are increasingly turning to alternative methods of verifying that keys are both valid and uncompromised. One method, product validation, assigns a product key based on a unique feature of the purchaser s computer hardware such as its MAC address, which cannot be as easily duplicated since it depends on the user s hardware. Other newer methods may involve requiring periodical validation of the CD key with an internet server for games with an online component, this is done whenever the user signs in. The validation can then be performed on the server side, preventing cracks tampering with it as they do on the client side. The server can also keep a blacklist of all CD keys known to be invalid or which have explicitly been banned, and deny them access.
Controversy edit
Some of the most effective CD key protection is very controversial, due to inconvenience, strict enforcement, harsh penalties and, in some cases, false positives. CD key protection has been likened to Digital Rights Management, by whom. in that it uses uncompromising digital procedures to enforce the license agreement.
Inconvenience edit
Product keys are somewhat inconvenient for end users. Not only do they need to be entered whenever a program is installed, but the user must also be sure not to lose them. Loss of a product key usually means the software is useless once uninstalled.
Product keys also present new ways for distribution to go wrong. If a product is shipped with missing or invalid keys, then the CD itself is useless. For example, all copies of Splinter Cell: Pandora Tomorrow originally shipped to Australia without CD keys. 1
Enforcement and penalties edit
There are many cases of permanent bans enforced by companies detecting usage violations. It is common for an online system to immediately blacklist a CD key caught running cracks or, in some cases, cheats. This results in a permanent ban. Players who wish to continue use of the software must repurchase it. This has inevitably led to criticism over the motivations of enforcing permanent bans. citation needed
Particularly controversial is the situation which arises when multiple products keys are bound together. If products have dependencies on other products as is the case with expansion packs, it is common for companies to ban all bound products. For example, if a fake CD key is used with an expansion pack, the server may ban legitimate CD keys from the original game. Similarly, with Valve s Steam service, all products the user has purchased are bound into the one account. If this account is banned, every product will be banned from online play. 2
This multi-ban is highly controversial, since it bans users from products which they have legitimately purchased and used. citation needed
False positives edit
Bans are enforced by servers immediately upon detection of cracks or cheats, usually without human intervention. Sometimes, legitimate users are wrongly deemed in violation of the license, and banned. In large cases of false positives, they are sometimes corrected as happened in World of Warcraft. 3 However, individual cases may not be given any attention. citation needed
A common cause of false positives as with the World of Warcraft case above is users of unsupported platforms. For example, users of Linux can run Windows applications through compatibility layers such as Wine and Cedega. This software combination sometimes triggers the game s server anti-cheating software, resulting in a ban due to Wine or Cedega being a Windows API compatibility layer for Linux, so it is considered third party cheating software by the game s server. 4 citation needed
Recovery of keys edit
A key recovery program is a program that is designed to read and decrypt and/or de-obfuscate the key to its original state. When the key is returned to its original state, it may be used to reinstall its corresponding software. 5
See also edit
Biometric passport
Cryptographic hash function
Intel Upgrade Service
Keygen
License manager
Product activation
Serial number
Software license server
Volume license key
References edit
Australian Pandora Tomorrow CD-Key Problems Shack News
Valve suspends 20,000 Steam accounts. GameSpot. Retrieved 2013-05-15.
Blizzard Unbans Linux World of Warcraft Players Softpedia
Linux users banned from Diablo 3- End Gamers
Retrieved from https://en.wikipedia.org/w/index.php.title Product_key oldid 697953189
Categories: Copyright infringement.
Upgrade to a product activation solution that is frictionless, secure, licensing modes software activation, Product Activation. Other software.